Gimli
Oct 20, 2019
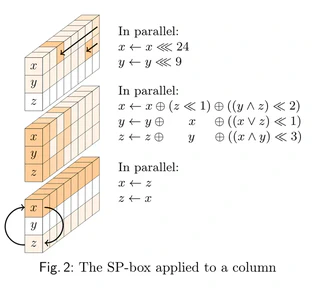
Gimli is a cryptographic permutation designed for high performance and security across a wide range of platforms. It is part of the NIST Lightweight Project and is integrated into LibHydrogen for efficient cryptographic operations.