Haraka - Efficient Short-Input Hashing for Post-Quantum Applications
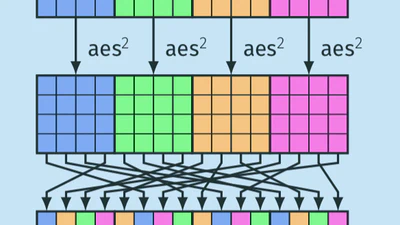
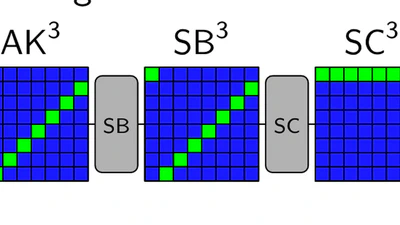
Recently, many efficient cryptographic hash function design strategies have been explored, not least because of the SHA-3 competition. These designs are, almost exclusively, geared …