Haraka v2 - efficient short-input hashing for post-quantum applications
Haraka - Efficient Short-Input Hashing for Post-Quantum Applications
Recently, many efficient cryptographic hash function design strategies have been explored, not least because of the SHA-3 competition. These designs are, almost exclusively, geared …
Troika: a ternary cryptographic hash function
Linear codes over finite fields are one of the most well-studied areas in coding theory. While codes over finite fields of characteristic two are of particular practical interest …
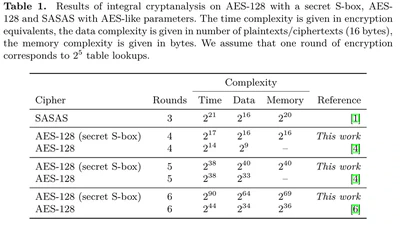
Practical attacks on AES-like Cryptographic Hash Functions
Practical Attacks on AES-like Cryptographic Hash Functions
Despite the great interest in rebound attacks on AES-like hash functions since 2009, we report on a rather generic, albeit keyschedule-dependent, algorithmic improvement: A new …
Differential Cryptanalysis of Keccak Variants
Differential Cryptanalysis of Keccak Variants
In October 2012, NIST has announced Keccak as the winner of the SHA-3 cryptographic hash function competition. Recently, at CT-RSA 2013, NIST brought up the idea to standardize …