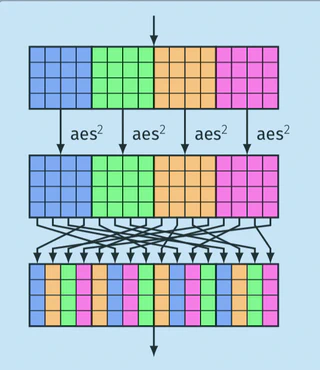
Haraka - Efficient Short-Input Hashing for Post-Quantum Applications

I am a Staff Engineer and Tech Lead Manager at Google, where I work in the Security Engineering team. My focus is on post-quantum cryptography and enabling developers at Google and across the internet to use cryptography safely and correctly.
I have a PhD in cryptography and an extensive background in the design and analysis of symmetric-key algorithms, post-quantum cryptography, and lightweight cryptography. I have contributed to several cryptographic standardization efforts, including the SKINNY cipher, which is part of the ISO/IEC 29192-2 standard. I also contributed to the SPHINCS+ signature scheme, which was standardized by NIST as FIPS 205. I currently represent Switzerland in the ISO/IEC JTC 1/SC 27/WG 2 committee for cryptography and security mechanisms.
Before joining Google, I was a Senior Technology Manager at Cybercrypt and a postdoctoral researcher at the Technical University of Denmark, working on the H2020 PQCRYPTO project.