ShiftRows Alternatives for AES-like Ciphers and Optimal Cell Permutations for Midori and Skinny
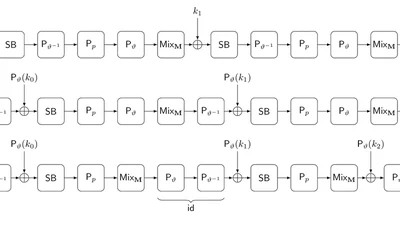
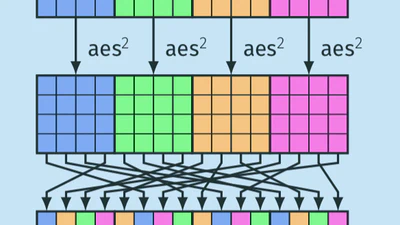
We study possible alternatives for ShiftRows to be used as cell permutations in AES-like ciphers. As observed during the design process of the block cipher Midori, when using a …
gianira-n.-alfarano